TheLatestTechNews Blog
Discover fresh ideas and expert opinions from our global community of guest authors and technology enthusiasts
 Read Full Article: How to Use an Age Verification System in Your Business?
Read Full Article: How to Use an Age Verification System in Your Business?How to Use an Age Verification System in Your Business?

|
Businesses use age verification systems to confirm the age of individuals accessing age-restricted products or services. It includes alcohol, tobacco, gambling, adult content, or specific…
 Read Full Article: Everything You Should Consider Before Selling Your Device
Read Full Article: Everything You Should Consider Before Selling Your DeviceEverything You Should Consider Before Selling Your Device

|
Technology is changing faster than expected. The latest gadget models are being released constantly and come with new, exciting functions and features. However, some people…
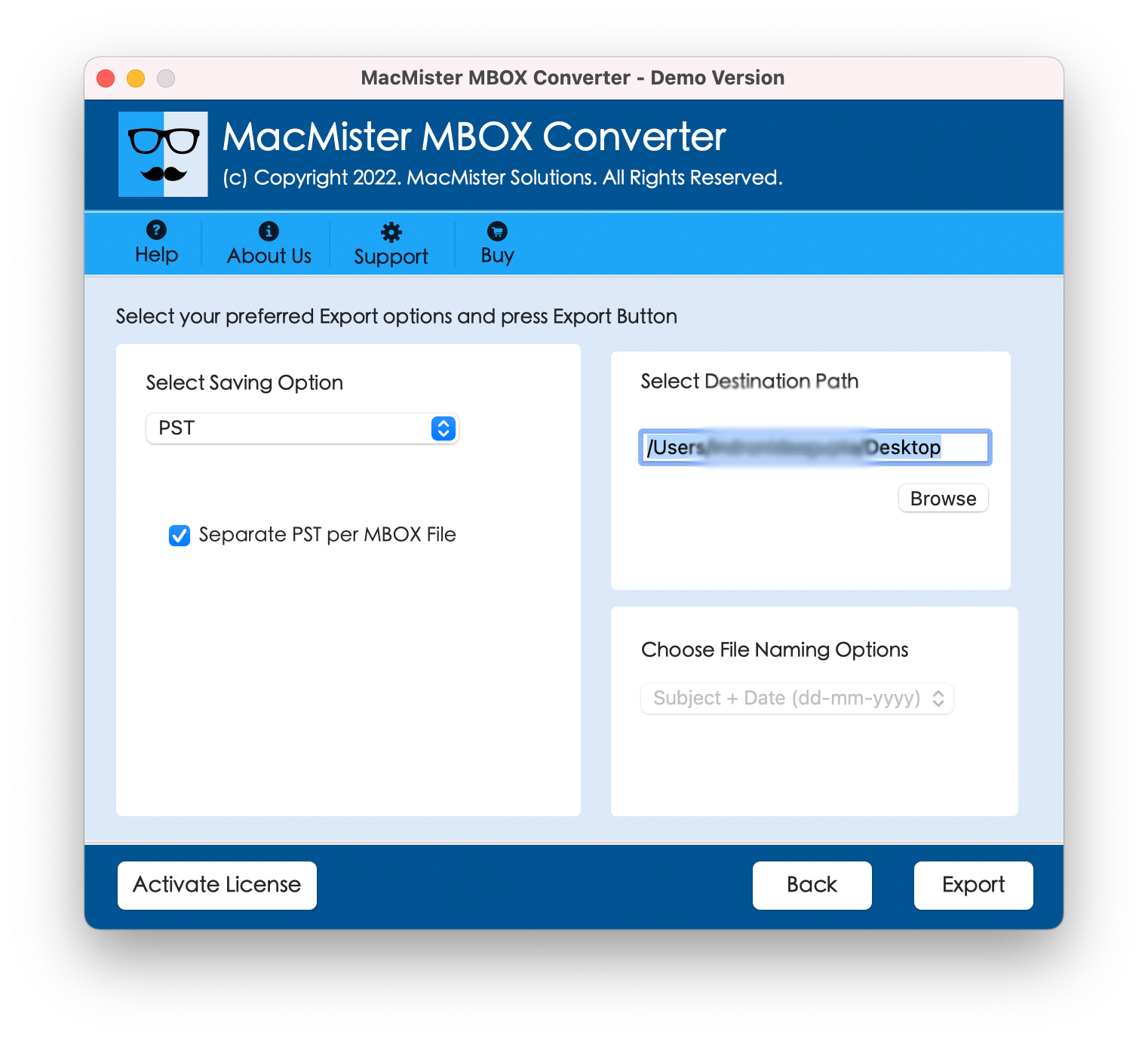 Read Full Article: How to See MBOX File of Apple Mail in Windows Outlook?
Read Full Article: How to See MBOX File of Apple Mail in Windows Outlook?How to See MBOX File of Apple Mail in Windows Outlook?

|
Have you recently moved to Windows from a Mac system and shifted to critical MBOX files? Need to urgently transfer them to Windows Outlook? Wondering…
 Read Full Article: Biometrics in Cyber Security: The Future of Secure Access?
Read Full Article: Biometrics in Cyber Security: The Future of Secure Access?Biometrics in Cyber Security: The Future of Secure Access?

|
In today’s increasingly digital world, cybersecurity has become paramount. Protecting our data, identities, and online assets is crucial, and traditional methods like passwords are becoming…
 Read Full Article: JEYI i9X Smart Display M.2 Dual Protocol SSD Enclosure: A Budget-Friendly Option?
Read Full Article: JEYI i9X Smart Display M.2 Dual Protocol SSD Enclosure: A Budget-Friendly Option?JEYI i9X Smart Display M.2 Dual Protocol SSD Enclosure: A Budget-Friendly Option?

|
Thinking of giving your computer a storage boost? The JEYI i9X Smart Display M.2 Dual Protocol SSD Enclosure from Banggood promises an easy way to…
 Read Full Article: Evaluating the ROI for Business Fibre Broadband and Leased Line Connection
Read Full Article: Evaluating the ROI for Business Fibre Broadband and Leased Line ConnectionEvaluating the ROI for Business Fibre Broadband and Leased Line Connection

|
In the modern digital world, businesses of all sizes require a fast, dependable internet connection to operate properly. To maintain productivity and efficiency at the…
 Read Full Article: Top Methods for Convert Outlook PST Files in Bulk to PDF
Read Full Article: Top Methods for Convert Outlook PST Files in Bulk to PDFTop Methods for Convert Outlook PST Files in Bulk to PDF

|
This article describes a flawless method by which an individual can effortlessly convert multiple PST files to PDF.
 Read Full Article: Understanding the Technology Behind Thermal Security Cameras and Their Applications
Read Full Article: Understanding the Technology Behind Thermal Security Cameras and Their ApplicationsUnderstanding the Technology Behind Thermal Security Cameras and Their Applications

|
In the realm of security and surveillance, thermal security cameras have emerged as a pivotal technology. These cameras, leveraging the power of infrared thermal imaging,…
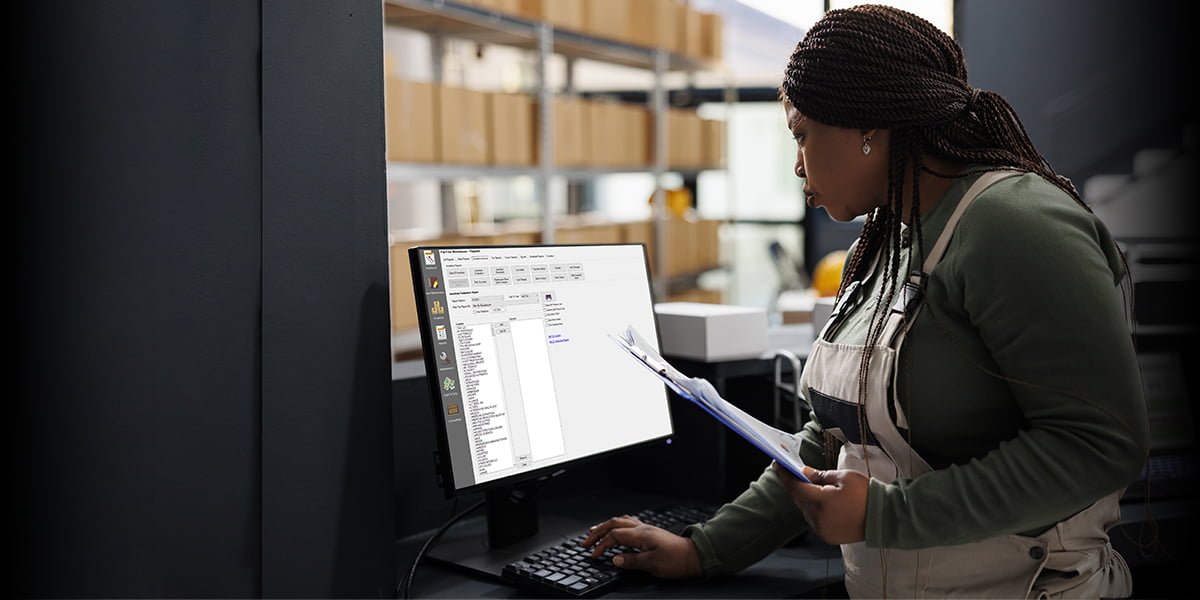 Read Full Article: Types of Inventory Management Systems
Read Full Article: Types of Inventory Management SystemsTypes of Inventory Management Systems

|
Inventory management is a crucial part of business operations. If your business isn’t doing it, chances are you’re leaving money on the table. The idea…
 Read Full Article: The Synergy Between Machine Learning and Data Science
Read Full Article: The Synergy Between Machine Learning and Data ScienceThe Synergy Between Machine Learning and Data Science

|
In the era of big data, machine learning, and data science have emerged as two closely related fields that are revolutionizing industries across the globe.…
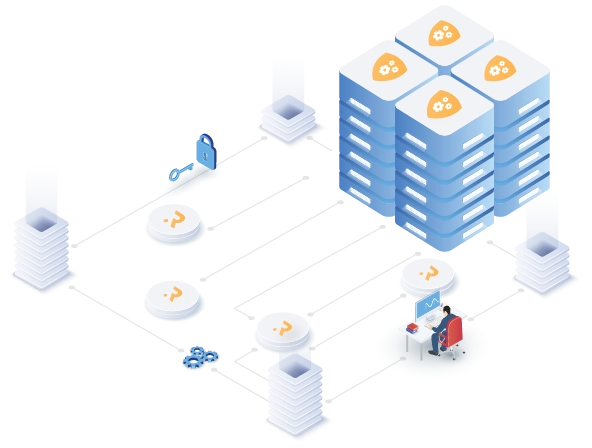 Read Full Article: Adaptive Load Balancing: Enhancing Performance in Dynamic Environments
Read Full Article: Adaptive Load Balancing: Enhancing Performance in Dynamic EnvironmentsAdaptive Load Balancing: Enhancing Performance in Dynamic Environments

|
In the context of modern networking, where digital landscapes are constantly evolving, the need for adaptive solutions that can seamlessly respond to fluctuating demands is…
 Read Full Article: Streamlining Email Management with Outlook: The Comprehensive Guide
Read Full Article: Streamlining Email Management with Outlook: The Comprehensive GuideStreamlining Email Management with Outlook: The Comprehensive Guide

|
This guide aims to provide solutions to common email management challenges, covering a wide range of topics from migrating between email clients to recovering lost…
